Information Security Initiatives
This page outlines our information security strategy, which is aligned with the ISO/IEC 27001 international standard, and describes the technical and operational frameworks that support it. Our approach prioritizes multi-layered technical defenses utilizing the principle of least privilege, ethical lifecycle management, and rigorous staff development to ensure cutting-edge security knowledge.


Confidentiality - The Foundation of Our Trust
As a group of visual media translation professionals, and guided by our philosophy of "Respecting language and honing our skills," we position the protection of our clients' confidential information as a top management priority. The integrity and security of the information entrusted to us is the bedrock of our credibility. We promise to reliably support the continuity of your business with an impregnable security structure.
POINT 1
Strategic Advantage:
Future-Focused Management Based on International Standards

Management and Operations Compliant with ISO/IEC 27001:2022
Our security strategy is built on the secure foundation of the international standard ISO/IEC 27001:2022, with its reliability proven through annual external audits.


ISO/IEC 27001 Certification
We acquired this certification in 2019, and transitioned to the latest standard (27001:2022) in 2024.

Scope of Management
We strictly manage all confidential information, including translation material and unreleased footage.

Assurance of Certainty
Annual external audits ensure the continued effectiveness of our ISMS certification.
Advanced Risk Management via ISO × NIST × Advanced Defense Strategy
We have adopted a "never trust, always verify" security model. This involves building our own advanced defense strategy based on ISO while also referring to strict international guidelines (NIST). By scrutinizing technical robustness based on ISO and referencing international defense guidelines (NIST), we are upgrading the entire process of risk identification, protection, detection, response, and recovery. Our goal is to strengthen our resilience against cyberattacks and reliably guarantee our clients' business continuity.

Cross-Departmental ISMS Committee
We approach information security as a strategic commitment across the entire organization. We have established a promotion structure that executes the PDCA cycle company-wide to continuously improve our systems and operations. We also emphasize human resource development to maintain the crisis awareness and expertise of all employees, enhancing our human defense capabilities.
POINT 2 Access Control and Multi-Layered Defense to Prevent Confidential Information Leakage

Least Privilege Management × Enhanced Authentication × Endpoint Protection
To protect our clients' data, we have adopted a policy focused on applying the highest level of control over access to and use of confidential information.
Principle of Least Privilege
Access privileges are strictly limited to the minimum required for business operations. Data is centrally managed in a company-approved storage system to prevent data dispersion. When an employee resigns or changes departments, their accounts and privileges are promptly suspended and deleted to ensure that unauthorized access is not possible.
Zero Trust Authentication and Multi-Layered Defense
Adopting the Zero Trust principle of "Never Trust, Always Verify," we strictly prevent unauthorized external access at the initial point of entry.

Authentication Assurance
Access to confidential information is controlled through Multi-Factor Authentication (MFA), ensuring continuous and reliable identity verification.

Network Defense
We have implemented UTM (Unified Threat Management) to consolidate security functions and reduce operational load. We block unauthorized external access and ensure threat detection through real-time monitoring.

Endpoint Protection
Company devices are equipped with security software to build defense layers including anti-malware measures. Proactive patching minimizes the risk of data breaches and system disruptions.
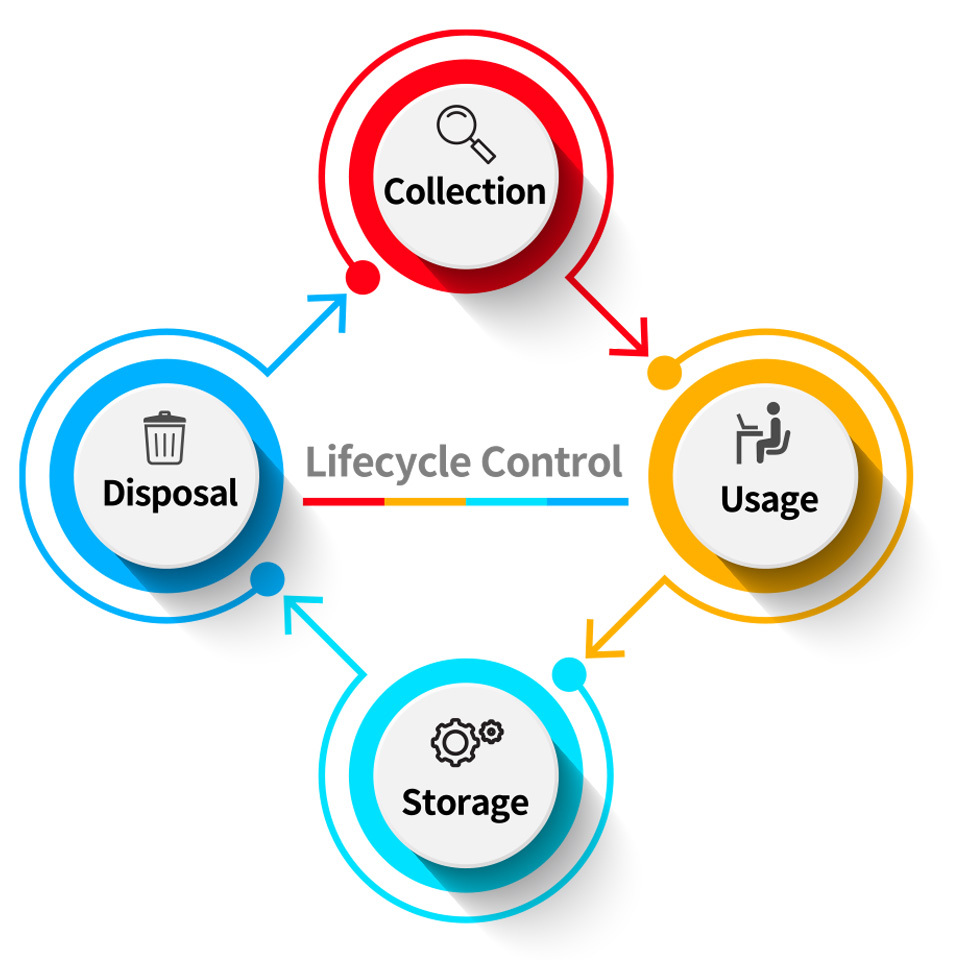
Legal Compliance and Lifecycle Control
We strictly execute the process from information collection to disposal based on professional ethics and responsibility. We control the information lifecycle (collection, storage, usage, and disposal) in accordance with laws and internal regulations, and we ensure that unnecessary data is completely erased using methods that make recovery impossible. External sharing requires the conclusion of an NDA and mandates the use of a link with restricted access.
POINT 3 Education, Audits, and Emergency Response to Minimize Human Risk

Fostering a Culture of Security Responsibility
We recognize that strengthening employees’ knowledge and their ability to respond quickly to crises is essential in addressing ever-evolving threats.
Education
We conduct regular training and comprehensive knowledge assessments for all employees and partners. We also mandate awareness training for students participating in our educational programs, aiming to establish the reduction of human risk as an organizational culture and maintain the knowledge level of the entire organization at the highest standard.

Internal Audits
We verify the effectiveness of our ISMS by objectively evaluating our operations through annual audits. Based on the audit results, we continuously implement improvements in each department to build a system that maintains the effectiveness of our structure.

Emergency Response
We have developed crisis response procedures and established a corresponding framework to ensure that operations are not impacted in a crisis event. We strengthen our initial response speed in the event of an emergency through annual disaster drills, cultivating the resilience to ensure our clients' operations do not stop even in unforeseen situations.

POINT 4 Continuous Security Commitment

As Professionals Dedicated to Protecting Trust
Through the continuous operation of our ISMS, we will continue to implement measures that stay one step ahead of the evolution of technology and threats. With robust systems and a high level of professionalism, we hereby make our final commitment to always maintaining the confidentiality, integrity, and availability of the precious information assets entrusted to us by our clients.